Modern commercial facilities demand sophisticated security solutions that balance protection with operational efficiency. Building access systems have evolved from simple lock-and-key mechanisms into intelligent networks that manage employee credentials, monitor entry points, and integrate with broader security infrastructures. For businesses across the UK, implementing robust access control represents a fundamental investment in protecting assets, ensuring regulatory compliance, and maintaining business continuity.
Understanding Building Access Systems in Commercial Environments
Building access systems form the frontline defence for commercial properties, controlling who enters specific areas and when. These solutions extend far beyond traditional locks, incorporating electronic credentials, biometric verification, and real-time monitoring capabilities.
A comprehensive system typically comprises several integrated components working in concert. Card readers or biometric scanners verify user credentials at entry points, whilst electric locks and door strikes physically control access. The control panel processes authentication requests and manages user permissions, and management software provides administrators with oversight and reporting capabilities.
Core Components and Their Functions
The architecture of modern building access systems relies on interconnected elements that create a secure perimeter:
- Credentials: Key cards, fobs, mobile credentials, or biometric identifiers
- Readers: Devices that scan and verify presented credentials
- Controllers: Processing units that make access decisions based on programmed rules
- Electric locks: Hardware that physically secures doors and responds to controller commands
- Management platform: Software interface for administration, monitoring, and reporting
Physical security experts emphasize the importance of designing access control systems with Security-in-Depth principles, creating multiple layers of protection throughout a facility. This approach ensures that even if one security measure fails, additional safeguards remain in place.

Technology Options for Commercial Facilities
Selecting the appropriate technology platform requires careful consideration of your facility's specific requirements, existing infrastructure, and long-term scalability needs.
Credential Technology Comparison
Different credential types offer varying levels of security, convenience, and cost-effectiveness:
| Credential Type | Security Level | Convenience | Implementation Cost | Best Use Cases |
|---|---|---|---|---|
| Proximity Cards | Moderate | High | Low | General employee access, high-traffic areas |
| Smart Cards | High | High | Moderate | Facilities requiring strong authentication |
| Biometric | Very High | Moderate | High | Sensitive areas, high-security zones |
| Mobile Credentials | High | Very High | Moderate | Tech-forward organizations, flexible workspaces |
| PIN Codes | Low-Moderate | Moderate | Low | Secondary verification, temporary access |
The selection process should account for user demographics, security requirements, and integration with existing systems. Many organizations adopt a hybrid approach, deploying different credential types across various security zones within a single facility.
Implementation Best Practices for Building Access Systems
Successful deployment requires methodical planning and stakeholder engagement throughout the process. Organizations must balance security requirements with operational practicality whilst ensuring compliance with relevant regulations.
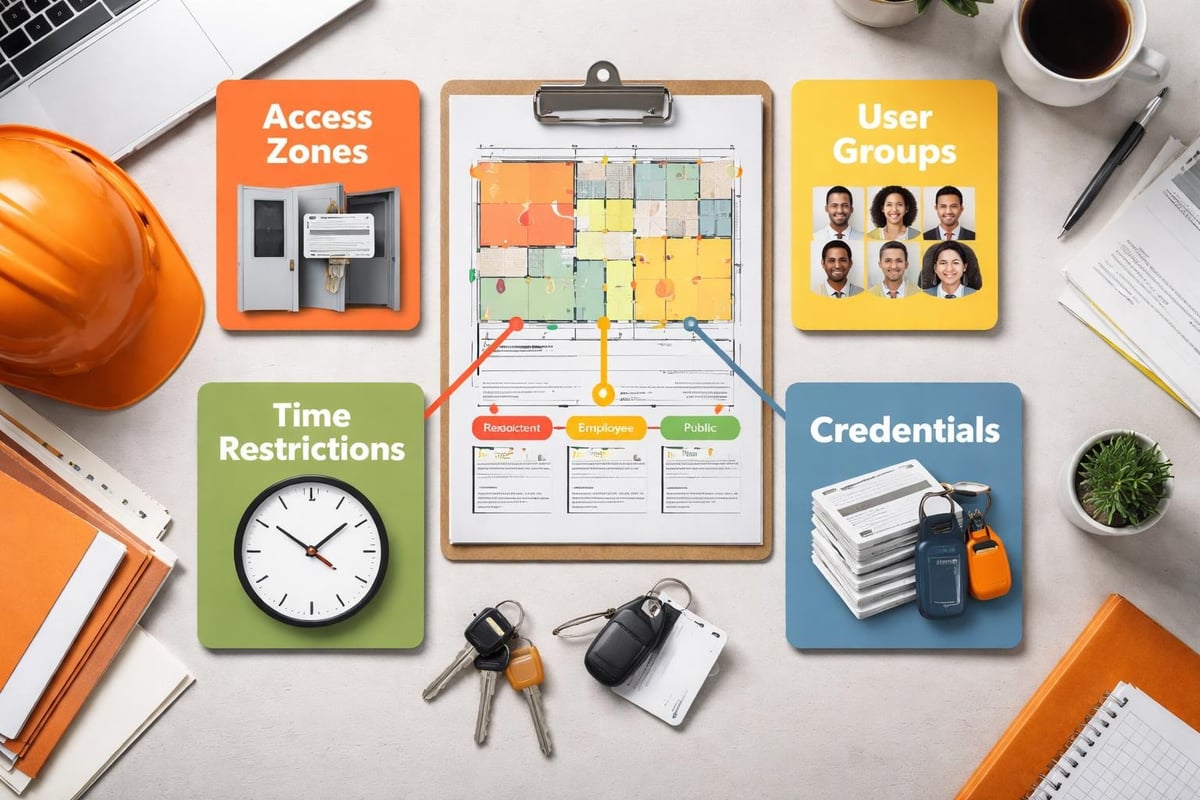
Planning and Design Considerations
Begin by conducting a comprehensive security assessment that identifies all entry points, defines security zones, and maps employee movement patterns. This foundational work informs decisions about hardware placement, credential distribution, and access policies.
- Map all entry points including primary entrances, loading docks, service entries, and emergency exits
- Define security zones with varying access requirements based on asset value and risk
- Identify user groups and establish appropriate permissions for each category
- Determine integration requirements with fire systems, CCTV, and intrusion detection
- Plan for scalability to accommodate future expansion and technology upgrades
Businesses implementing commercial access control systems benefit from partnering with experienced integrators who understand the complexities of multi-system environments. Professional installation ensures proper configuration, reliable operation, and compliance with building codes.
Access Policy Development
Establishing clear, documented access policies forms the backbone of effective security management. These policies should define who receives credentials, what areas they can access, and under what conditions access may be granted or revoked.
Principle of least privilege should guide policy development. Employees receive only the minimum access necessary to perform their duties, reducing exposure if credentials are compromised. Regular reviews ensure permissions remain appropriate as roles change.
Consider implementing time-based restrictions that automatically limit access during non-business hours or grant temporary permissions for contractors and visitors. Advanced systems can enforce anti-passback rules preventing credential sharing and mustering capabilities for emergency evacuation scenarios.
Integration with Fire Safety and Security Systems
Building access systems operate most effectively when integrated with complementary security technologies, creating a unified platform for facility management. This convergence enables coordinated responses to security events and streamlines administrative workflows.
Fire System Integration Requirements
Fire safety regulations mandate that building access control systems do not impede emergency egress. Integration with fire alarm systems ensures automatic unlocking of access-controlled doors when alarms activate, allowing safe evacuation whilst maintaining security during normal operations.
Professional security providers like those offering comprehensive fire and security solutions ensure proper coordination between access control and fire detection systems. This integration must comply with British Standards and building regulations whilst preserving the integrity of both systems.
Key integration points include:
- Automatic door unlock on fire alarm activation
- Elevator recall and lobby control during emergencies
- Integration with emergency lighting and evacuation systems
- Coordination with smoke door release mechanisms
- Fail-safe configurations ensuring life safety takes precedence
Video Surveillance and Intrusion Detection
Pairing access control with surveillance security systems provides visual verification of entry events and creates comprehensive audit trails. When credentials are presented, cameras can capture images for later review, whilst video analytics can identify tailgating attempts or unusual activity patterns.
Intrusion detection systems add another layer by monitoring for forced entry attempts, door-held-open violations, and after-hours activity. Integrated platforms present alerts from all systems through a unified interface, enabling security personnel to respond efficiently to incidents.
Operational Management and Maintenance
Ongoing management determines whether building access systems deliver sustained value or become administrative burdens. Organizations must establish processes for credential lifecycle management, system maintenance, and security policy enforcement.
Credential Administration Workflows
Efficient credential management requires defined processes for issuance, modification, and revocation. When employees join the organization, access provisioning should follow documented procedures that grant appropriate permissions based on role and department.
Automated workflows can streamline routine tasks. Integration with human resources systems enables automatic credential deactivation when employees terminate, eliminating security gaps from manual processes. Regular audits identify orphaned credentials and ensure permissions remain aligned with current responsibilities.
Best practices for managing access control systems emphasize the importance of maintaining accurate user databases and conducting periodic access reviews. These practices prevent permission creep and ensure accountability.
System Maintenance and Testing
Regular maintenance preserves system reliability and identifies potential failures before they compromise security. Scheduled activities should include:
- Monthly testing of door hardware, readers, and electric locks
- Quarterly review of access logs and unusual activity patterns
- Annual inspection of wiring, power supplies, and backup batteries
- Software updates to patch security vulnerabilities and add functionality
- User training to ensure proper credential handling and security awareness
Organizations should maintain detailed documentation of system configuration, wiring diagrams, and maintenance records. This information proves invaluable during troubleshooting and facilitates efficient updates as the system evolves.
Advanced Features and Emerging Technologies
Modern building access systems incorporate sophisticated capabilities that extend beyond basic entry control, providing data insights and operational efficiencies that benefit broader organizational objectives.
Mobile Credentials and Contactless Access
The shift toward mobile credentials accelerates as smartphones become ubiquitous. Bluetooth Low Energy (BLE) and Near Field Communication (NFC) technologies enable credential storage on mobile devices, eliminating physical cards and enhancing user convenience.
Mobile platforms offer additional advantages including remote credential issuance, temporary access for visitors, and integration with workplace applications. Users can unlock doors, book meeting rooms, and access building services through a single application.
Implementation considerations include device compatibility, battery management, and fallback options for users without smartphones. Security teams must also address the implications of lost or stolen devices and ensure robust authentication protects mobile credentials.
Analytics and Intelligence
Contemporary platforms generate vast quantities of data about building usage patterns, peak traffic times, and space utilisation. Analytics tools transform this raw data into actionable insights that inform facility management decisions.
| Analytics Application | Business Value | Key Metrics |
|---|---|---|
| Occupancy tracking | Space optimization, energy management | Real-time headcount, zone utilisation |
| Traffic flow analysis | Entrance efficiency, queuing reduction | Peak times, bottleneck identification |
| Security forensics | Incident investigation, compliance | Access logs, credential usage patterns |
| Predictive maintenance | Equipment reliability, cost reduction | Door cycle counts, reader performance |
| Regulatory compliance | Audit readiness, risk mitigation | Access attempts, policy violations |

Regulatory Compliance and Standards
Commercial building access systems must satisfy various regulatory requirements depending on industry sector, facility type, and the nature of assets being protected. Understanding applicable standards ensures deployments meet legal obligations whilst following recognized best practices.
Industry-Specific Requirements
Financial institutions, healthcare facilities, and data centres face sector-specific regulations governing physical security controls. The Financial Conduct Authority (FCA), Care Quality Commission (CQC), and Information Commissioner's Office (ICO) all publish guidance affecting access control implementations in their respective domains.
Organizations handling sensitive information must demonstrate appropriate physical safeguards as part of broader information security frameworks. ISO 27001 certification often requires documented access control policies, regular audits, and evidence of effective implementation.
Data Protection Considerations
Building access systems collect and process personal data, triggering obligations under the UK General Data Protection Regulation (UK GDPR). Organizations must establish lawful bases for processing, implement appropriate security measures, and respect individual rights regarding their data.
Key compliance requirements include:
- Privacy notices explaining data collection and usage
- Data retention policies limiting storage duration
- Access controls restricting who can view system data
- Audit trails documenting system administration activities
- Procedures for responding to subject access requests
Working with security providers who understand security and access control regulatory landscapes ensures compliant implementations that withstand scrutiny from regulators and auditors.
Cost Considerations and Return on Investment
Investing in building access systems requires balancing upfront costs against long-term value, considering both direct security benefits and operational efficiencies that extend beyond loss prevention.
Budget Components and Pricing Models
Total cost of ownership encompasses hardware, software licensing, installation labour, and ongoing maintenance. Understanding these components enables accurate budgeting and prevents unexpected expenses.
Initial investment includes:
- Control panels and door hardware
- Credentials and reader devices
- Management software licenses
- Installation and configuration services
- Training for administrators and users
Recurring costs comprise:
- Annual software maintenance and support
- Replacement credentials for lost or damaged items
- Preventive maintenance and inspections
- System upgrades and capacity expansion
- Staff time for system administration
Organizations can realize return on investment through reduced security incidents, elimination of rekeying costs, improved operational efficiency, and enhanced regulatory compliance. Many businesses find that access systems pay for themselves within three to five years through these combined benefits.
Selecting Implementation Partners
The complexity of modern building access systems makes professional implementation essential for most commercial deployments. Choosing the right partner significantly influences project success, system reliability, and long-term satisfaction.
Evaluating Security Integrators
Look for providers with demonstrable experience in commercial installations, relevant industry certifications, and comprehensive service offerings spanning design through ongoing support. Organizations should verify credentials, review project portfolios, and speak with existing clients about their experiences.
Essential qualifications include:
- NSI or SSAIB accreditation for security installations
- Manufacturer certifications for specified equipment
- Professional indemnity and public liability insurance
- Proven track record with similar facility types
- 24/7 support availability for critical systems
Established providers offering commercial security systems typically maintain relationships with multiple manufacturers, enabling technology-agnostic recommendations aligned with client needs rather than vendor preferences. This independence ensures solutions match requirements rather than forcing requirements to fit available products.
Service and Support Expectations
Post-installation support determines whether systems continue delivering value or become sources of frustration. Clarify service level agreements, response times, and escalation procedures before committing to partnerships.
Critical support elements include helpdesk availability, on-site response commitments, spare parts inventory, and proactive maintenance programs. The best providers offer monitoring services that identify issues before users report problems, minimizing disruption and maintaining security effectiveness.
Future-Proofing Your Investment
Technology evolution continues accelerating, making today's cutting-edge solutions tomorrow's legacy systems. Strategic planning and architectural decisions during initial implementation can extend system lifespan and protect technology investments.
Scalability and Flexibility
Design systems with growth in mind, selecting platforms that accommodate additional doors, users, and features without requiring complete replacement. Cloud-based management systems offer particular advantages for scalability, eliminating on-premises server capacity constraints.
Design considerations for future expansion:
- Controller capacity exceeding immediate requirements
- Network infrastructure supporting additional devices
- Software licensing models accommodating user growth
- Open protocols enabling third-party integrations
- Modular architecture supporting phased upgrades
Industry experts recommend improving building access control systems through regular technology assessments that identify opportunities for enhancements and ensure continued alignment with organizational needs.
Technology Refresh Cycles
Even well-maintained systems eventually require replacement as hardware ages and software support ends. Planning technology refresh cycles prevents emergency replacements whilst taking advantage of improved capabilities in newer platforms.
Most commercial installations benefit from major upgrades every 7-10 years, with interim component replacements as needed. Budgeting for these cycles ensures organizations can invest strategically rather than reactively responding to failures.
Building access systems represent critical infrastructure for modern commercial facilities, protecting assets whilst enabling efficient operations and regulatory compliance. Successful implementations require careful planning, professional installation, and ongoing management to deliver sustained value. Whether upgrading existing systems or deploying new infrastructure, partnering with experienced providers ensures solutions meet both current requirements and future needs. Logic Fire and Security brings extensive experience designing and implementing integrated security solutions for businesses across the UK, combining technical expertise with understanding of commercial operational requirements to deliver systems that enhance both security and efficiency.