Selecting the right fire alarm supply partner represents one of the most critical decisions facing facilities managers and building owners across the United Kingdom. The complexities of modern fire detection systems demand not only high-quality components but also reliable suppliers who understand compliance requirements, product specifications, and long-term maintenance needs. Whether upgrading an existing system or specifying equipment for a new installation, understanding the landscape of fire alarm supply ensures your organisation maintains optimal safety standards whilst managing costs effectively.
Understanding Fire Alarm Supply Chain Components
The fire alarm supply industry encompasses a diverse range of manufacturers, distributors, and specialist providers who deliver everything from basic detection devices to sophisticated integrated systems. At the foundation level, suppliers must stock essential components including smoke detectors, heat sensors, manual call points, sounders, and control panels. These individual elements form the building blocks of any fire detection installation.
Quality fire alarm supply extends beyond simple product availability. It encompasses technical support, product certification, compatibility assurance, and ongoing availability of replacement parts. Leading suppliers maintain comprehensive inventories that include both contemporary technology and legacy components, ensuring facilities can maintain existing systems whilst planning strategic upgrades.
Key Components in Modern Fire Alarm Supply
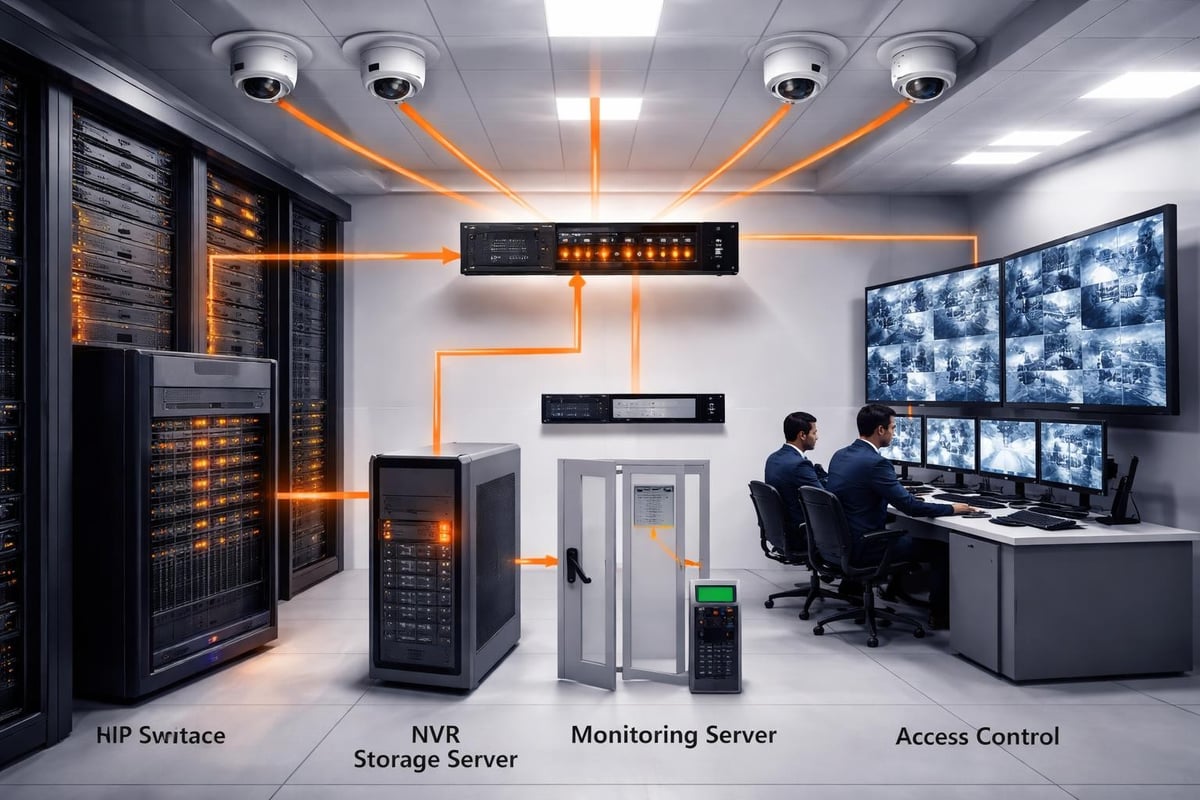
Professional fire alarm supply operations typically categorise their offerings into several distinct groups:
- Detection devices: Optical smoke detectors, ionisation detectors, heat detectors, multi-sensor units, and beam detectors
- Control and indication equipment: Fire alarm control panels, repeater panels, network devices, and mimic panels
- Warning devices: Bells, sounders, visual alarm devices (VADs), and voice evacuation speakers
- Manual devices: Break glass call points and remote test devices
- Interface modules: Input/output modules, relay modules, and integration devices
- Power supplies: Battery units, chargers, and power supply modules
The breadth of this inventory highlights why selecting an experienced fire alarm supply partner proves essential for commercial installations. Systems must comply with BS 5839 Part 1, the British standard governing fire detection and alarm systems in non-domestic premises, which specifies stringent requirements for component quality and system design.
Evaluating Fire Alarm Supply Partnerships
Establishing relationships with dependable fire alarm supply companies protects organisations from project delays, compliance failures, and long-term maintenance challenges. The selection process should examine multiple factors beyond initial pricing, as the true value of a supplier emerges through sustained partnership and support.
Critical Selection Criteria
When assessing potential fire alarm supply partners, facilities managers should evaluate several fundamental aspects of their operations:
| Criterion | Why It Matters | What to Verify |
|---|---|---|
| Product range | Ensures compatibility and choice | Manufacturer partnerships, stock levels |
| Technical expertise | Supports specification and troubleshooting | Qualifications, training programmes |
| Compliance knowledge | Guarantees regulatory adherence | Certification status, standards awareness |
| Delivery reliability | Prevents project delays | Stock management, logistics capabilities |
| After-sales support | Ensures long-term system performance | Warranty terms, technical helpline |
Experience within your specific sector matters considerably. A fire alarm supply company serving commercial offices, healthcare facilities, educational establishments, and manufacturing sites understands the unique requirements each environment presents. This sector-specific knowledge informs product recommendations and system specifications, reducing the risk of inappropriate component selection.
The importance of choosing the right fire alarm system vendor cannot be overstated, as this decision influences system performance, compliance status, and total cost of ownership throughout the installation's operational lifetime. Companies like Logic Fire and Security have built their reputation on understanding these complex requirements across diverse commercial environments.
Standards Compliance in Fire Alarm Supply
Regulatory compliance represents a non-negotiable aspect of fire alarm supply in the United Kingdom. Every component supplied for commercial fire detection systems must meet established standards, with documentation proving conformity to relevant European and British specifications.
European and British Standards Framework
The EN 54 series of standards governs fire detection and fire alarm equipment across Europe. This comprehensive framework covers individual component types, from control panels (EN 54-2) to smoke detectors (EN 54-7) and manual call points (EN 54-11). Fire alarm supply companies must verify that all products carry appropriate EN 54 certification marks before distribution.
British Standards provide additional guidance specific to UK installations. BS 5839-1:2017 establishes the code of practice for system design, installation, commissioning, and maintenance in non-domestic buildings. Professional fire alarm supply partners maintain current knowledge of these standards, advising clients on compliant component selection and system configuration.
Additional standards influence fire alarm supply decisions:
- BS 7671 (IEC 60364) for electrical installations
- BS 8629 for evacuation alert systems serving people with disabilities
- Building Regulations Approved Document B for fire safety provisions
- Fire Safety Order 2005 requirements for risk assessment and appropriate systems
Organisations requiring guidance on compliance frameworks should consult resources on codes and standards that outline the regulatory landscape governing fire detection equipment.
Advanced System Integration and Supply Considerations
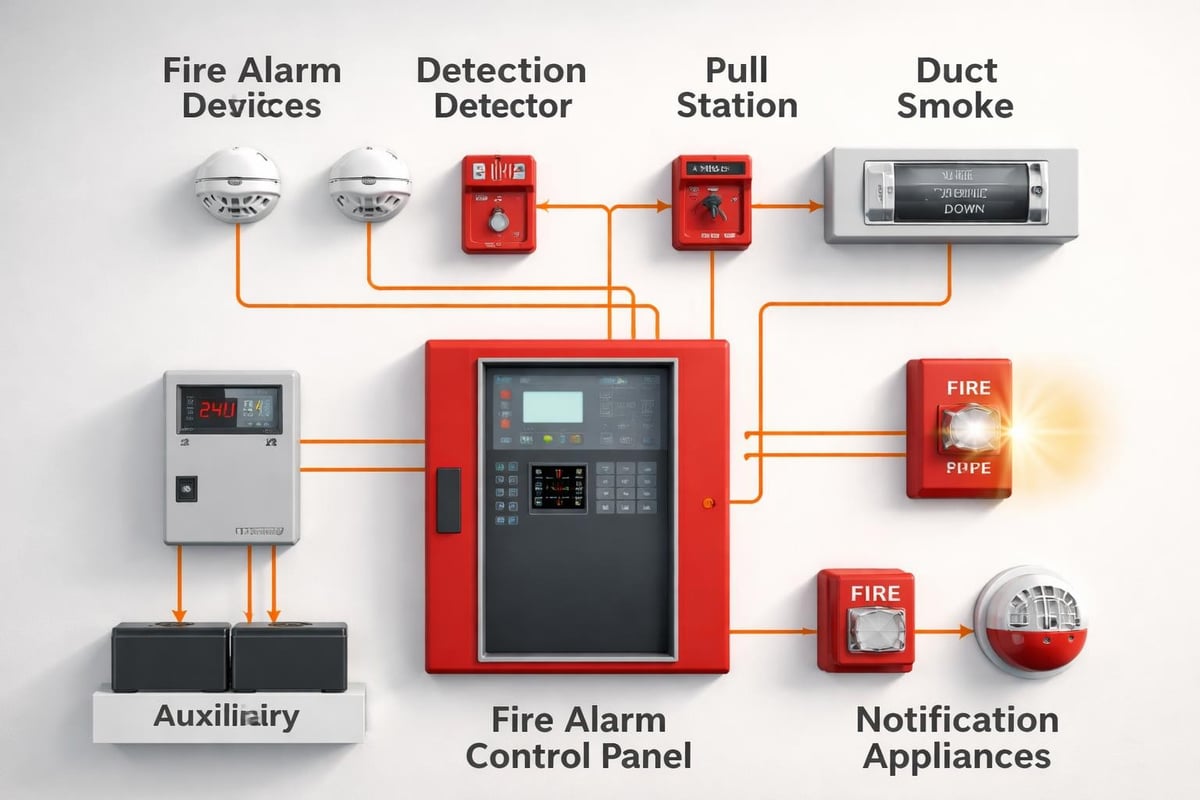
Modern fire alarm supply extends beyond standalone detection systems to encompass integrated solutions that connect fire safety with broader building management infrastructure. This integration demands suppliers who understand network protocols, software platforms, and compatibility requirements across diverse manufacturers.
Networked and Addressable Systems
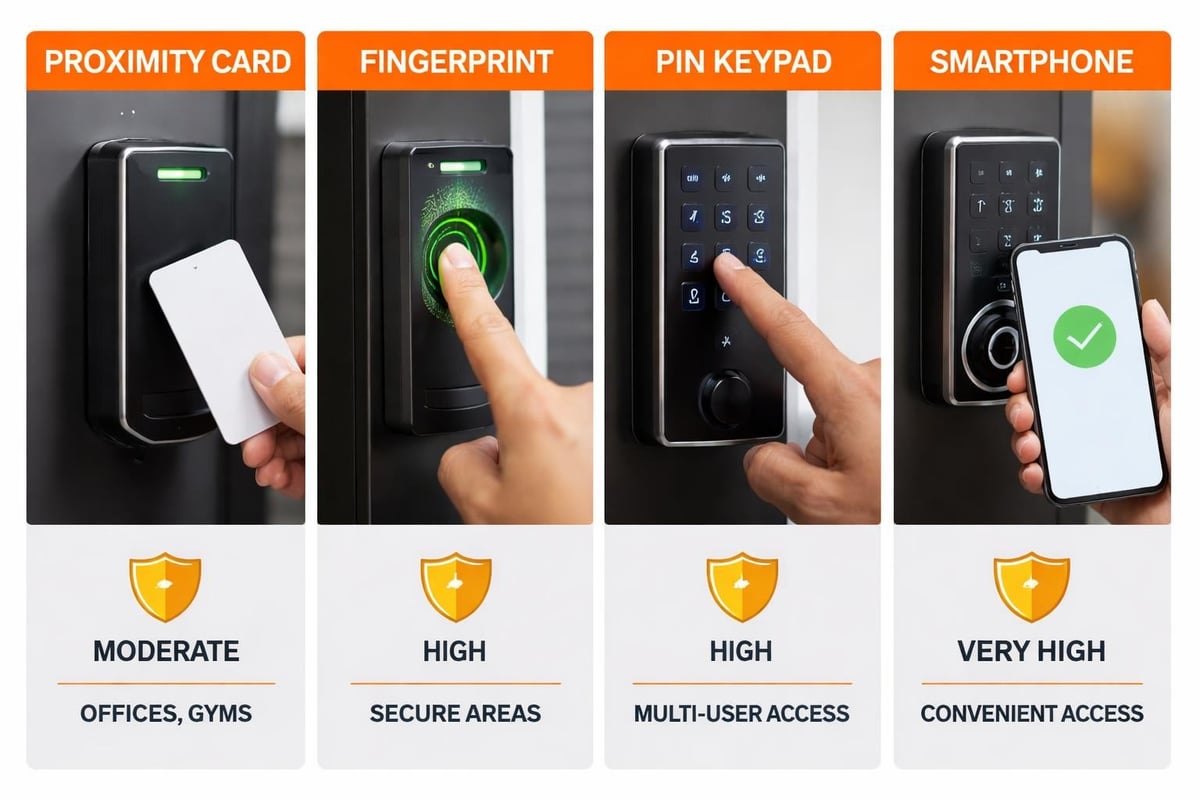
Contemporary commercial installations predominantly specify addressable fire alarm systems, where each detection device carries a unique identifier on the network. This architecture enables precise fault location, individual device monitoring, and sophisticated cause-and-effect programming. Fire alarm supply for addressable systems requires careful attention to compatibility, as mixing components from different manufacturers often creates integration challenges.
Protocol compatibility represents a critical consideration. Whilst some manufacturers employ proprietary communication standards, others utilise open protocols that facilitate multi-vendor integration. Suppliers who understand these technical distinctions guide clients toward solutions that balance performance, flexibility, and cost-effectiveness.
Integration extends to connections with other building systems:
- Building Management Systems (BMS): Fire alarm data feeds into centralised monitoring platforms
- Access control: Automatic door release upon fire alarm activation
- HVAC systems: Smoke control and air handling coordination
- Emergency lighting: Synchronised activation with fire alarm signals
- Voice evacuation: Phased evacuation messaging coordinated with alarm zones
For organisations implementing comprehensive safety strategies, exploring commercial security systems demonstrates how fire alarm supply decisions fit within broader security infrastructure planning.
Maintenance Planning and Long-Term Supply Relationships
The relationship with a fire alarm supply partner extends throughout the system's operational life, which typically spans fifteen to twenty-five years. Successful maintenance programmes depend upon reliable access to replacement components, technical support, and system knowledge that suppliers provide.
Obsolescence Management
Technology evolution creates ongoing challenges for facilities managers. Components become obsolete as manufacturers discontinue product lines, requiring careful planning to maintain system functionality. Proactive fire alarm supply partners notify clients of impending obsolescence, offering migration pathways that minimise disruption and cost.
Strategic approaches to obsolescence management include:
- Maintaining critical spare parts inventories for current systems
- Planning phased upgrades rather than complete system replacement
- Selecting manufacturers with demonstrated long-term product support
- Documenting system configurations to facilitate future modifications
- Establishing service level agreements that guarantee component availability
Professional maintenance arrangements, such as those provided through fire alarm monitoring services, often include supply agreements ensuring rapid access to replacement components during fault resolution.
Quality Assurance in Fire Alarm Supply
Distinguishing between genuine manufacturer products and substandard alternatives demands rigorous quality assurance processes. Reputable fire alarm supply companies implement verification procedures that protect clients from counterfeit components, ensuring every device meets specification requirements.
Certification and Traceability
Each component should carry traceable certification documentation. This includes manufacturer certificates of conformity, third-party testing reports, and compliance declarations referencing relevant EN 54 standards. Fire alarm supply chains that maintain comprehensive documentation enable clients to demonstrate regulatory compliance during inspections and audits.
| Quality Indicator | Verification Method | Risk if Absent |
|---|---|---|
| CE marking | Visual inspection, documentation review | Non-compliance, insurance issues |
| EN 54 certification | Certificate verification, LPCB approval | System rejection, failed commissioning |
| Batch traceability | Serial number records, supply chain documentation | Warranty complications, recall management |
| Performance data | Test certificates, specification sheets | Inappropriate application, system failure |
Following best practices for fire and gas detection includes verifying that all supplied components originate from authenticated sources and carry appropriate certification marks.

Installation Support and Technical Resources
Effective fire alarm supply partnerships extend beyond component delivery to encompass technical guidance, installation support, and commissioning assistance. Suppliers who invest in technical resources help installers avoid common fire alarm installation mistakes that compromise system performance and compliance.
Design and Specification Support
Professional fire alarm supply companies employ technical specialists who review project requirements, recommend appropriate components, and verify design compliance with applicable standards. This consultative approach proves particularly valuable for complex installations involving multiple protection categories, diverse environmental conditions, or specialised detection requirements.
Technical support typically encompasses:
- System architecture recommendations and network topology planning
- Device selection based on environmental conditions and risk assessment
- Power supply calculations ensuring adequate capacity for full system operation
- Cable specification guidance for different zones and circuit types
- Integration planning for connections with other building systems
Organisations seeking to improve documentation accuracy benefit from understanding how to improve fire alarm design documents, ensuring specifications accurately communicate requirements to fire alarm supply providers.
Emerging Technologies in Fire Alarm Supply
The fire alarm supply sector continues evolving as manufacturers introduce innovative detection technologies, connectivity solutions, and intelligent algorithms that enhance system performance. Staying informed about technological developments enables facilities managers to specify solutions that deliver long-term value.
Wireless and Hybrid Systems
Wireless fire alarm technology has matured significantly, offering reliable alternatives to traditional hard-wired installations. Fire alarm supply for wireless systems includes radio-frequency devices, repeaters, and gateways that create mesh networks capable of serving substantial commercial premises. These solutions prove particularly valuable during refurbishment projects where minimising disruption and avoiding cable installation costs deliver significant benefits.
Hybrid configurations combine wired and wireless technologies, allowing facilities to extend existing systems or add coverage to challenging areas without comprehensive rewiring. Progressive fire alarm supply partners maintain expertise across both traditional and wireless platforms, recommending optimal approaches based on building characteristics and budget considerations.
Recent innovations reshaping fire alarm supply include:
- Multi-sensor detectors: Combining optical, heat, and carbon monoxide detection in single devices
- Cloud connectivity: Remote monitoring and diagnostics through internet-connected panels
- Video verification: Camera integration providing visual confirmation of alarm conditions
- AI algorithms: Machine learning reducing false alarms through intelligent signal analysis
- Mobile applications: Commissioning and testing tools simplifying installation and maintenance
Facilities exploring comprehensive safety solutions should investigate how fire alarm systems integrate with complementary technologies including emergency lighting, evacuation systems, and disabled refuge provisions.
Cost Management and Value Optimisation
Whilst initial component costs influence fire alarm supply decisions, sophisticated procurement strategies consider total cost of ownership throughout the system lifecycle. This broader perspective examines installation efficiency, maintenance requirements, energy consumption, and upgrade pathways.
Life-Cycle Cost Analysis
Evaluating fire alarm supply options through life-cycle costing reveals the true financial impact of component selection. Premium products often deliver superior reliability, reducing maintenance callouts and replacement frequencies that accumulate substantial costs over time. Similarly, energy-efficient devices lower operational expenses, whilst systems designed for easy expansion reduce future modification costs.
A comprehensive cost comparison should evaluate:
| Cost Category | Budget Products | Premium Products | Long-Term Impact |
|---|---|---|---|
| Initial purchase | Lower | Higher | Initial budget allocation |
| Installation time | Standard | Potentially faster | Labour cost variation |
| False alarm rate | Higher potential | Lower through advanced algorithms | Reduced disruption, compliance costs |
| Maintenance frequency | More frequent | Extended intervals | Ongoing service expenses |
| Component lifespan | 10-15 years | 15-25 years | Replacement cycle costs |
| Upgrade compatibility | Limited | Future-proof design | System longevity, modification costs |
Strategic fire alarm supply partnerships help organisations balance immediate budget constraints against long-term value creation, identifying solutions that optimise both safety performance and financial outcomes.
Sector-Specific Fire Alarm Supply Considerations
Different commercial sectors present unique fire alarm supply requirements reflecting their operational characteristics, regulatory frameworks, and risk profiles. Suppliers with sector expertise understand these nuances, recommending solutions appropriately tailored to specific environments.
Healthcare Facilities
Medical establishments demand fire alarm systems that balance patient safety with operational continuity. Fire alarm supply for healthcare environments includes specialist devices such as zone-indicating call points that direct staff to incident locations, and sounders with volume profiles that alert occupants without causing unnecessary distress to vulnerable patients.
Educational Institutions
Schools, colleges, and universities require robust systems capable of withstanding demanding environments whilst providing clear evacuation guidance across complex building layouts. Fire alarm supply specifications often emphasise vandal-resistant devices, voice evacuation capabilities for phased evacuation, and integration with security systems managing access control.
Industrial and Manufacturing
Production facilities present challenging detection environments featuring heat, dust, fumes, and electromagnetic interference. Specialist fire alarm supply for industrial applications includes high-temperature detectors, beam detection for large open spaces, and explosion-proof devices rated for hazardous atmospheres.
Commercial Offices and Retail
Office buildings and retail premises typically implement sophisticated addressable systems with graphical indication, allowing security teams to monitor extensive sites from centralised control rooms. Understanding fire risk assessment requirements helps specify appropriate detection coverage and system capabilities.
Supplier Relationships and Partnership Benefits
Establishing enduring relationships with fire alarm supply providers delivers advantages extending beyond transactional component purchases. Strategic partnerships facilitate knowledge transfer, preferential pricing, priority support, and collaborative approaches to system optimisation.
Value-Added Services
Leading fire alarm supply companies differentiate themselves through comprehensive service offerings that support clients throughout the project lifecycle. These value-added capabilities transform suppliers into trusted advisers who contribute to safety outcomes rather than merely fulfilling component orders.
Partnership benefits typically include:
- Technical training for facilities management teams and maintenance personnel
- Specification review services validating designs against standards and best practices
- Stock management programmes ensuring critical spares availability
- Scheduled maintenance planning coordinating inspections with component replacement cycles
- System health monitoring identifying performance trends and predicting failures
- Compliance updates communicating regulatory changes affecting installed systems
For organisations seeking comprehensive support, engaging specialists who provide fire alarm monitoring alongside component supply ensures integrated approaches to fire safety management.
Documentation and Compliance Recording
Comprehensive documentation represents a fundamental requirement for compliant fire alarm installations, with records demonstrating that supplied components meet specifications and systems function as designed. Fire alarm supply partners contribute to documentation requirements through certificates, test data, and product information.
Essential Documentation
Every fire alarm supply transaction should generate appropriate documentation supporting compliance verification and future maintenance activities. This paperwork establishes an audit trail demonstrating due diligence in component selection and system specification.
Critical documents include:
- Manufacturer certificates of conformity to EN 54 standards
- Technical datasheets specifying device performance characteristics
- Installation instructions and wiring diagrams
- Commissioning certificates confirming system functionality
- Operation and maintenance manuals for end-user reference
Following fire alarm inspection best practices requires maintaining accessible records that inspectors can review during routine assessments and compliance audits.
Selecting the right fire alarm supply partner fundamentally influences the safety, compliance, and operational effectiveness of commercial fire detection systems throughout their service life. By prioritising quality, compliance expertise, technical support, and long-term partnership potential, organisations establish robust foundations for protecting people and property. Logic Fire and Security combines comprehensive product knowledge with decades of installation and maintenance experience, helping businesses across the United Kingdom specify, source, and maintain fire detection systems that deliver reliable performance whilst meeting stringent regulatory requirements.