Modern businesses face unprecedented security challenges that demand sophisticated protection strategies. Commercial access control systems have evolved from simple lock-and-key mechanisms into intelligent networks that manage who enters your premises, when they enter, and what areas they can access. These systems form a critical component of comprehensive security infrastructure, particularly for organisations handling sensitive data, valuable assets, or regulatory compliance requirements.
Understanding Commercial Access Control Technology
Commercial access control systems represent a fundamental shift in how organisations approach physical security. Rather than relying on traditional keys that can be copied, lost, or stolen, these systems use electronic credentials to verify identity and grant permissions based on predetermined rules.
The architecture of commercial access control systems typically includes several interconnected components working together seamlessly. At the heart of every system lies a control panel or server that processes authentication requests, stores user credentials, and maintains comprehensive audit logs. Door readers positioned at entry points communicate with this central intelligence, whilst electronic locks respond to authorised access attempts.

Core Components and Infrastructure
Every effective access control solution comprises specific hardware and software elements that must work in harmony. The control panel serves as the brain of the operation, processing thousands of authentication requests whilst maintaining system integrity and security protocols.
Essential hardware components include:
- Door readers (card, biometric, or keypad)
- Electronic strikes, magnetic locks, or electrified mortise locks
- Request-to-exit sensors and door position switches
- Power supplies and backup battery systems
- Network infrastructure connecting all devices
Modern systems integrate seamlessly with existing commercial security systems to create unified protection platforms. This integration enables coordinated responses to security events, such as automatically locking all doors during a fire alarm activation or triggering CCTV monitoring when unauthorised access attempts occur.
Credential Types and Authentication Methods
Selecting appropriate credential technology directly impacts both security effectiveness and user convenience. The market offers numerous options, each with distinct advantages suited to different operational requirements and risk profiles.
Traditional and Proximity Cards
Proximity cards remain popular due to their affordability and ease of deployment. These credentials operate using radio frequency identification (RFID) technology, communicating with readers when brought within range. However, standard proximity cards can be vulnerable to cloning, making them less suitable for high-security environments.
Smart cards incorporating encrypted chips provide enhanced security through mutual authentication protocols. These credentials exchange encrypted data with readers, making unauthorised duplication significantly more difficult. Many organisations deploy smart cards that serve dual purposes, functioning as both access credentials and employee identification badges.
Biometric Authentication Systems
Biometric readers verify identity through unique physical characteristics that cannot be easily transferred, shared, or stolen. Fingerprint scanners represent the most common biometric deployment, offering a balance between security, cost, and user acceptance.
| Biometric Type | Security Level | Speed | Cost | Best Application |
|---|---|---|---|---|
| Fingerprint | High | Fast | Moderate | General access, high-traffic areas |
| Facial Recognition | Very High | Very Fast | High | Executive areas, sensitive zones |
| Iris Scanning | Extremely High | Moderate | Very High | Maximum security facilities |
| Hand Geometry | Moderate | Fast | Moderate | Industrial environments |
Facial recognition technology has advanced considerably, now capable of operating effectively in varying lighting conditions whilst preventing spoofing attempts. These systems excel in environments requiring touchless authentication, a consideration that gained prominence following health and safety concerns.
Mobile Credentials and Digital Keys
The transition to smartphone-based credentials reflects broader digital transformation trends across industries. Mobile access control leverages Bluetooth Low Energy (BLE) or Near Field Communication (NFC) technology, allowing users to unlock doors using their smartphones.
This approach offers several compelling advantages for organisations seeking operational flexibility. Credentials can be issued, modified, or revoked instantly through cloud-based management platforms, eliminating physical card distribution logistics. Temporary access for contractors, visitors, or deliveries becomes straightforward, with time-limited digital keys sent via email or SMS.
System Architecture and Deployment Models
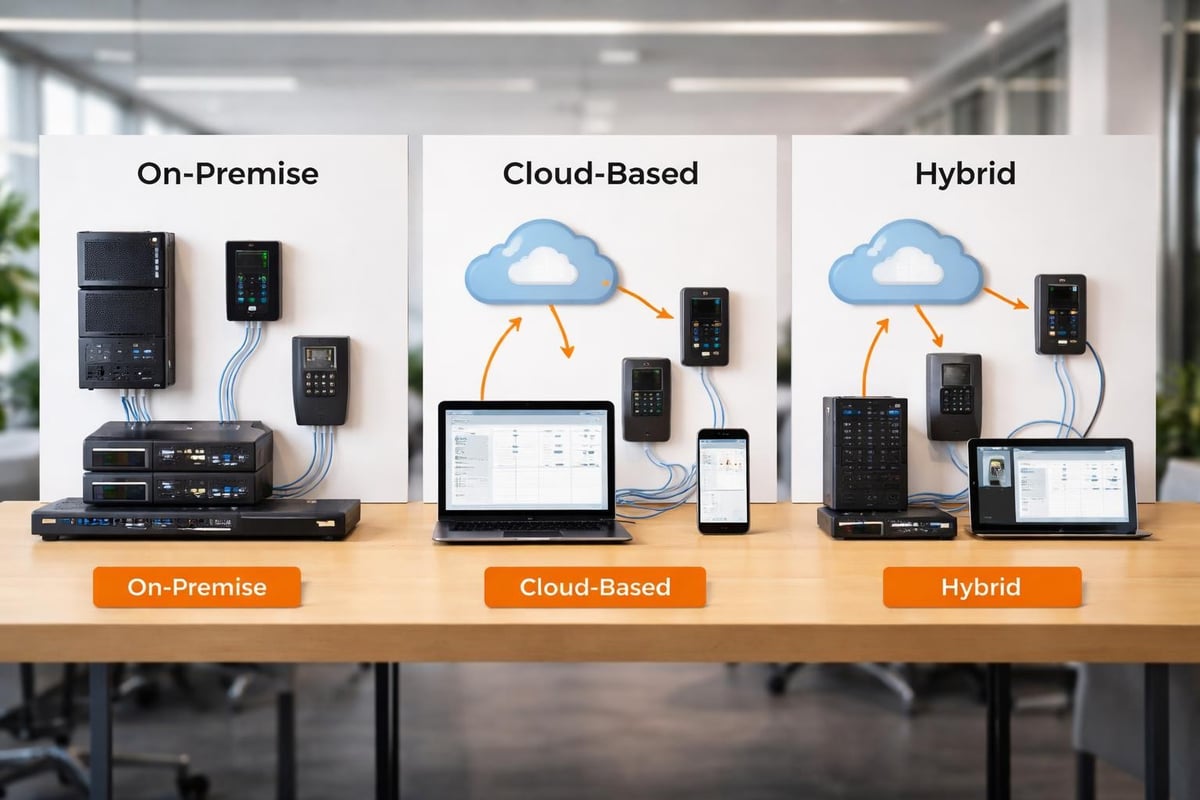
Organisations must evaluate different architectural approaches when implementing commercial access control systems. Each deployment model presents unique characteristics affecting scalability, maintenance requirements, and total cost of ownership.
On-Premise Solutions
Traditional on-premise systems house all control hardware and software within the protected facility. A dedicated server runs access control software, whilst all readers and locks connect through wired or wireless networks managed entirely by the organisation.
This architecture provides complete data sovereignty, with all credentials and audit logs remaining under direct organisational control. Many organisations in regulated industries prefer this approach due to compliance requirements or policies prohibiting cloud-based data storage.
On-premise systems offer:
- Complete control over security policies and data
- No recurring cloud subscription fees
- Operation during internet outages
- Integration with existing IT infrastructure
- Customisation opportunities for unique requirements
However, on-premise deployments require significant upfront investment in servers, software licences, and networking infrastructure. Organisations must also maintain technical expertise for system administration, updates, and troubleshooting.
Cloud-Based Access Control
Cloud-based platforms have transformed how organisations approach access control deployment and management. These systems shift processing and data storage to secure data centres operated by specialised providers, whilst door hardware connects to cloud servers via internet gateways.
The advantages of cloud-based business access control systems become particularly evident for organisations operating multiple locations. Administrators can manage users, view real-time activity, and modify permissions across all sites through unified web-based interfaces accessible from any internet-connected device.
| Feature | On-Premise | Cloud-Based |
|---|---|---|
| Initial Investment | High | Low |
| Scalability | Limited by hardware | Highly scalable |
| Remote Management | Requires VPN | Native capability |
| Maintenance | Internal IT required | Vendor managed |
| Multi-site Management | Complex | Streamlined |
| Offline Functionality | Full operation | Limited operation |
Hybrid Architectures
Forward-thinking organisations increasingly adopt hybrid approaches combining on-premise and cloud elements. These systems maintain local control panels ensuring door operation during connectivity disruptions, whilst leveraging cloud platforms for management, reporting, and advanced analytics.
Hybrid architectures deliver operational resilience alongside modern management capabilities. Critical security functions continue operating locally, whilst administrators enjoy the convenience and accessibility of cloud-based tools for routine management tasks.
Integration with Building Management Systems
The true power of commercial access control systems emerges through strategic integration with complementary security and building management technologies. Rather than operating as isolated silos, modern systems communicate with fire alarms, CCTV networks, intruder detection, and building automation platforms.
When fire alarm monitoring detects smoke or heat, integrated access control systems respond automatically by releasing magnetic locks on egress doors, ensuring safe evacuation routes remain accessible. This coordination proves essential for regulatory compliance and occupant safety.
Integration with commercial CCTV systems enables security teams to correlate access events with video footage. When someone badges into a restricted area, the system automatically retrieves corresponding camera feeds, creating comprehensive audit trails that prove invaluable during investigations.
Advanced Integration Scenarios
Sophisticated implementations extend beyond basic security integration to encompass broader building management functions. Access control systems can communicate with heating, ventilation, and air conditioning (HVAC) systems, adjusting environmental controls based on occupancy patterns detected through badge events.
Integration opportunities include:
- Automatic lighting control triggered by access events
- Lift access restricted by floor based on credentials
- Visitor management systems for streamlined guest processing
- Time and attendance tracking for payroll accuracy
- Parking management and space allocation
These integrations transform access control from purely security tools into comprehensive building intelligence platforms. The unified platform approach reduces administrative overhead whilst providing valuable operational insights through aggregated data analysis.
User Management and Access Policies
Effective access control extends beyond hardware selection to encompass thoughtful policy development and user administration. Organisations must establish clear frameworks defining who accesses which areas under what circumstances, then implement these policies through system configuration.
Role-Based Access Control
Role-based access control (RBAC) simplifies administration by grouping users according to their organisational functions. Rather than configuring permissions individually for each person, administrators create access levels corresponding to job roles, then assign users to appropriate groups.
A facilities management company might establish distinct access levels for executives, administrative staff, maintenance personnel, and visitors. Executives receive unrestricted building access, whilst maintenance staff access mechanical rooms and plant areas but not executive offices. This approach maintains security whilst streamlining user administration.
- Define organisational roles and corresponding access requirements
- Create access levels matching each role’s legitimate needs
- Assign users to appropriate groups based on their function
- Review and update permissions during role changes or transfers
- Conduct regular audits ensuring policy compliance
Time-Based Restrictions
Temporal restrictions add another security dimension by controlling when credentials remain valid. Standard employees might access facilities during business hours, whilst cleaning crews receive overnight permissions. Contractors receive temporary credentials valid only for project duration.
These time-based controls reduce security exposure by automatically preventing access outside authorised periods. The system maintains detailed logs of all access attempts, flagging unusual patterns such as after-hours entry by personnel without explicit authorisation.
Compliance and Audit Requirements
Numerous industries face regulatory requirements demanding comprehensive access control documentation and audit capabilities. Healthcare organisations must comply with patient privacy regulations, financial institutions answer to data protection mandates, whilst government contractors navigate strict security clearance protocols.
Commercial access control systems generate detailed audit trails recording every badge event, door opening, and system configuration change. These logs capture who accessed which doors, when access occurred, whether entry was granted or denied, and which credentials were used.
The importance of audit trails cannot be overstated for organisations subject to compliance audits. Regulatory bodies expect comprehensive documentation demonstrating appropriate access controls and the ability to trace all facility entry. Modern systems maintain these records indefinitely, with reporting tools enabling rapid retrieval during investigations or audits.
Data Protection Considerations
Commercial access control systems collect and store personal information, creating data protection obligations under regulations such as the UK General Data Protection Regulation (UK GDPR). Organisations must implement appropriate safeguards protecting credential data, access logs, and personally identifiable information.
Security best practices include encrypting all stored data, implementing strong authentication for system administrators, and restricting access to audit logs based on legitimate business needs. Regular security assessments identify potential vulnerabilities before they can be exploited.

Scalability and Future-Proofing
Organisations must consider long-term requirements when selecting commercial access control systems, as these installations typically serve businesses for decades. Systems should accommodate growth, technological advancement, and evolving security needs without requiring complete replacement.
Planning for Expansion
Scalable architectures allow organisations to add doors, users, and locations without fundamental system changes. Cloud-based platforms excel in this regard, as organisations simply purchase additional door licences or expand user counts through subscription modifications.
On-premise systems require more careful capacity planning, ensuring control panels, servers, and network infrastructure can support anticipated growth. Modular hardware designs allow incremental expansion, adding controllers and readers as needed whilst maintaining the existing foundation.
Scalability considerations include:
- Maximum door count supported by control panels
- User capacity limitations and expansion costs
- Network infrastructure requirements for additional readers
- Software licensing models and upgrade paths
- Integration capabilities with emerging technologies
Technology Evolution and Standards
The access control industry continues evolving, with innovations in mobile credentials, biometrics, artificial intelligence, and cloud computing reshaping capabilities. Organisations should prioritise systems supporting open standards and application programming interfaces (API), enabling integration with future technologies.
Selecting systems from established manufacturers with strong research and development commitments helps ensure ongoing support, security updates, and compatibility with emerging trends. The various types of commercial access control systems available today demonstrate the importance of choosing vendors committed to long-term innovation.
Professional Installation and Ongoing Support
Whilst some manufacturers market plug-and-play access control solutions, professional installation by experienced security integrators proves essential for reliable, compliant deployments. Complex systems involving multiple doors, integration requirements, and compliance obligations demand technical expertise that extends beyond basic product knowledge.
Qualified installers understand proper hardware mounting, network configuration, power supply sizing, and fail-safe versus fail-secure lock operation. They ensure systems meet building codes, fire safety regulations, and accessibility requirements whilst optimising performance for specific operational needs.
The relationship with security partners extends well beyond initial installation. Ongoing support encompasses regular maintenance, software updates, troubleshooting, and system optimisation. Organisations benefit from establishing partnerships with providers like Logic Fire and Security who offer comprehensive lifecycle support.
Maintenance and System Health
Commercial access control systems require periodic maintenance ensuring continued reliability and security. Regular inspections verify reader functionality, test electronic locks, confirm backup power operation, and validate network connectivity.
Software maintenance proves equally critical, with manufacturers regularly releasing updates addressing security vulnerabilities, adding features, and improving performance. Organisations must implement structured update procedures testing patches before production deployment whilst maintaining system documentation.
Essential maintenance activities include:
- Monthly testing of all door hardware and readers
- Quarterly battery backup verification
- Bi-annual comprehensive system health assessments
- Annual security audits and penetration testing
- Continuous monitoring of system alerts and notifications
Establishing service level agreements with qualified providers ensures predictable support costs whilst guaranteeing rapid response when issues arise. The 247 protection offered through professional monitoring services provides additional assurance that access control systems receive immediate attention during malfunctions or security events.
Cost Considerations and Return on Investment
Understanding the total cost of ownership for commercial access control systems requires examining both initial investment and ongoing operational expenses. Whilst upfront costs often receive primary attention during procurement, long-term expenses significantly impact overall value.
| Cost Category | On-Premise | Cloud-Based |
|---|---|---|
| Hardware | £500-£1,500 per door | £300-£1,000 per door |
| Software Licensing | £5,000-£25,000+ | Included in subscription |
| Installation | £150-£400 per door | £150-£400 per door |
| Annual Maintenance | £500-£2,000 | Included in subscription |
| Monthly Subscription | £0 | £20-£100 per door |
| System Administration | Internal IT costs | Reduced requirements |
Beyond direct expenditure, organisations should evaluate operational benefits contributing to return on investment. Access control systems eliminate costs associated with rekeying locks after employee departures, reduce security staffing requirements through automation, and prevent losses from unauthorised access or theft.
Enhanced operational efficiency represents another value dimension. Automated visitor management reduces reception workload, whilst integration with time and attendance systems streamlines payroll processing. These efficiency gains accumulate over system lifespan, often justifying initial investment within several years.
Selecting the Right System for Your Organisation
Choosing appropriate commercial access control systems demands careful evaluation of organisational requirements, operational constraints, and strategic objectives. No single solution suits all organisations, making thorough needs assessment essential before procurement decisions.
Key Selection Criteria
Begin by documenting specific security requirements, considering both current needs and anticipated future developments. Organisations handling sensitive information require more robust authentication than those protecting standard office environments. Similarly, facilities with high visitor volumes demand different capabilities than those primarily serving employees.
Critical evaluation factors include:
- Number of doors requiring control
- Types of credentials preferred (cards, biometrics, mobile)
- Integration requirements with existing security systems
- Compliance obligations and audit capabilities
- Budget constraints and total cost of ownership
- Scalability for anticipated growth
- Vendor reputation and support capabilities
Industry-specific considerations also influence system selection. Healthcare facilities prioritise patient privacy and emergency access procedures, whilst educational institutions emphasise safety during lockdown scenarios. Manufacturing environments require durable hardware withstanding harsh conditions, whilst corporate offices focus on aesthetics and user experience.
Vendor Evaluation Process
Selecting qualified vendors proves as important as choosing appropriate technology. The relationship with access control providers extends across decades, making vendor stability, expertise, and service quality essential evaluation criteria.
Request detailed proposals from multiple qualified providers, ensuring specifications address all documented requirements. Evaluate not only pricing but also implementation methodology, training provisions, warranty terms, and ongoing support commitments. Reference checks with existing clients provide valuable insights into vendor performance and reliability.
Understanding the comprehensive guide to commercial access control systems helps organisations ask informed questions during vendor discussions, ensuring proposals address critical requirements and identify potential limitations before commitment.
Commercial access control systems represent essential infrastructure for modern organisations seeking to protect people, assets, and information whilst maintaining operational efficiency. The combination of sophisticated technology, thoughtful policy development, and professional implementation creates security environments that adapt to evolving threats and organisational needs. For businesses across the UK requiring comprehensive security solutions, Logic Fire and Security delivers expert access control design, installation, and ongoing support backed by decades of experience serving Blue Chip companies and public agencies.